Jaden Furtado.
A Cybersecurity Engineer, Hacker, Artist, and Musician, trying to make the world a better place :)

About me
I'm an offensive security engineer at R.U.D.R.A Cybersecurity Pvt. Ltd. I have a passion for coding and a love for pure maths (and Manchester United!). I spend my time building and breaking stuff, finding and reporting vulnerabilities in software used by private and government organizations. Feel free to reach out to me regarding anything security or tech related.
My Skills
Cybersecurity is a huge domain and I by no means claim to "Know it all"! However, the below are a few sub-domains that I have previously done.
Vulnerability Assessment and Penetration Testing
Code Reviews
OT and IoT security audits
Network security audits
Dev-sec Ops
Application Development
Music :)
Some of my Talks
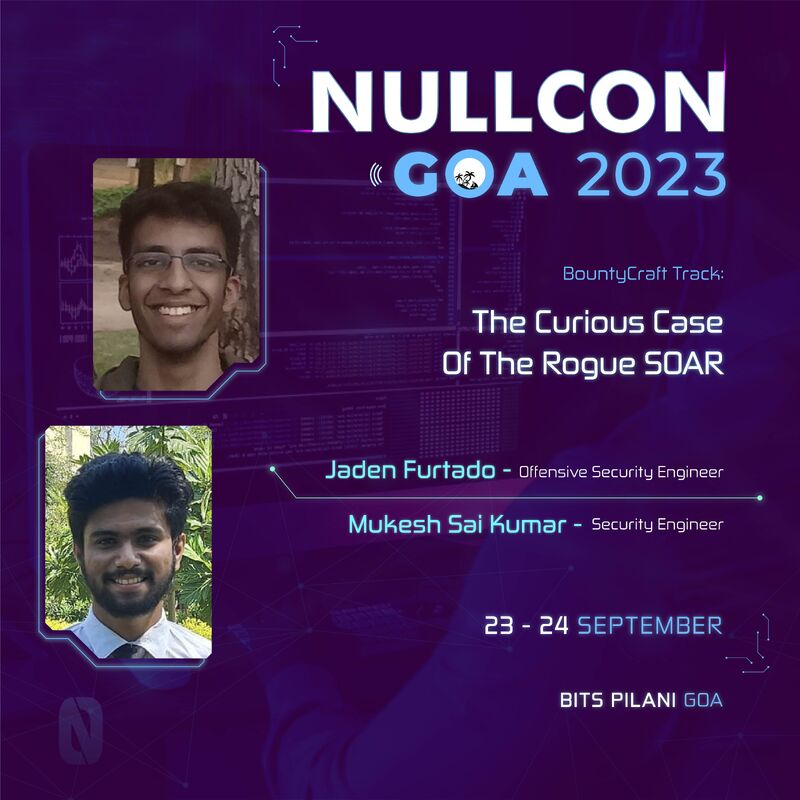
The Curious Case of The Rogue SOAR: NullCon Goa 2023
The smart enemy attacks you exactly where you think you are safe. Most attacks try and target a server or a service being used by a company. But when the attack targets the very SOAR tool you use to defend your network to break in, things get interesting. Given that SOAR tools would be whitelisted in an organization to be able to capture logs from various servers and devices, the consequences of such vulnerabilities being exploited are far-reaching. On successful exploitation, either by the methods we’ve shown or from some other similar vectors, it would result in the complete compromise of the network as well as internal devices and services which are often present in large corporate networks. It also foreshadows future attacks via log poisoning on SOCs and SOAR tools that make use of LLMs such as ChatGPT leading to possible prompt injections.
Hacking Trains NullCon Berlin 2024
This started as a joke when a colleague shared an article about railways getting hacked. As an exercise in OSINT, I decided to try and find everything I could on the railways, for a laugh. From the interactions I’ve had, “It can’t happen to us because we’ve met compliance. That’s just the way things are!” is the way executives usually approach cybersecurity issues in this industry.
The things we wanted to find a definitive answer to were:
A: Is it possible for a low-skilled attacker to gain remote access, via the public internet, to sensitive systems of the railways?
B: If yes, what is the worst thing that an attacker could achieve using this access?
C: Finally, how difficult is it to pull this off? Can we prove that a novice with a few hours could replicate our work?
What we uncovered was, interesting...
Lights Out SINCON 2024
In January, a team of 4 OT hackers from RUDRA spent 14 days on the road, driving over 5,000km through 7 states. Their mission was to conduct detailed technical assessments of power and energy infrastructure. The proposed talk will be done by members of this team who worked on dozens of active power plants and energy transmission infrastructure. The narrative will cover some interesting attack vectors, a complete ICS Cyber Kill Chain over the Internet using a zero-touch Zero-Day exploit that was performed by the team. In addition to the main mission of hacking power plants, the team setup radio equipment on this vehicle to war-drive across the entire country, profiling every cell tower, every bluetooth beacon and WiFi network that they came across.
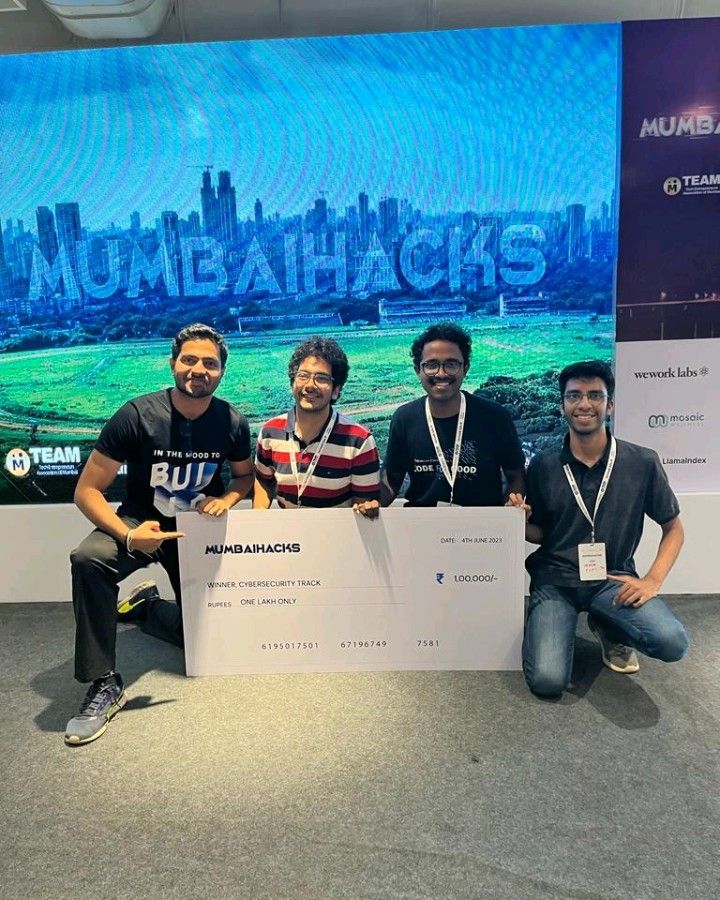
From the Archives